How it works:
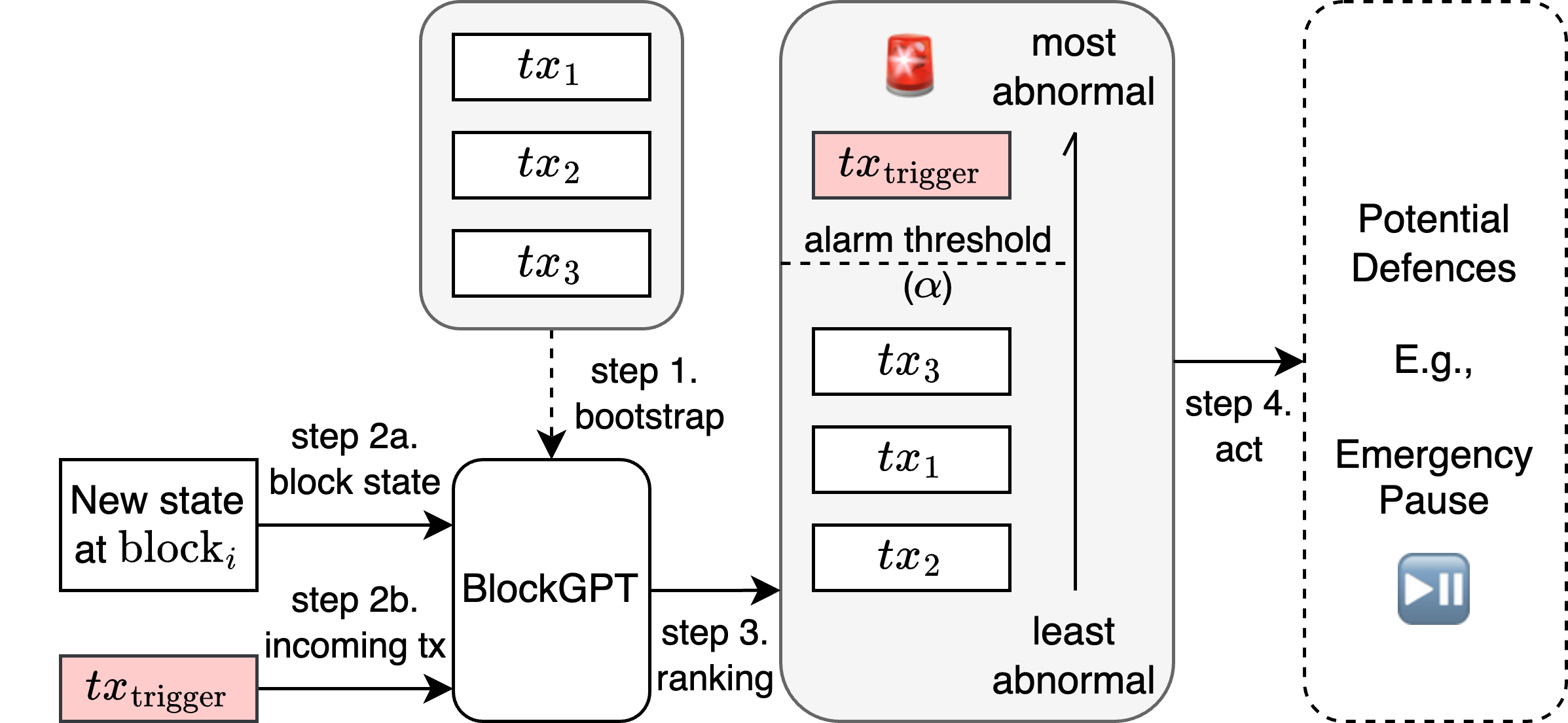
High-level overview of the BlockGPT defense mechanism, which consists of the following four major steps. ➊ BlockGPT is bootstrapped by feeding in a dataset of historical transactions to train the model using unsupervised learning. ➋ Depending on the system and threat model, BlockGPT detects new block states, including already confirmed transactions, and pending transactions. ➌ BlockGPT ranks transactions based on how abnormal their execution traces are. ➍ If an abnormal transaction is detected , BlockGPT triggers a defense mechanism such as a front-running emergency pause.