“SoK: Decentralized Finance (DeFi) Attacks”
2023 | Liyi Zhou · Xihan Xiong · Jens Ernstberger · Stefanos Chaliasos · Zhipeng Wang · Ye Wang · Kaihua Qin · Roger Wattenhofer · Dawn Song · Arthur Gervais | https://arxiv.org/abs/2208.13035
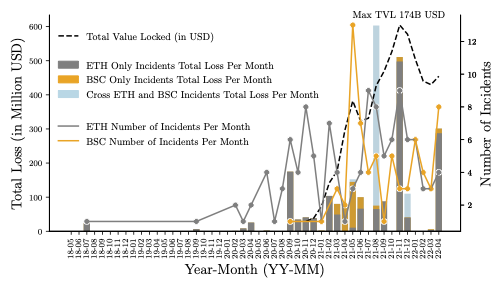
We investigate 77 academic papers, 30 audit reports, and 181 real-world incidents. Our open data reveals several gaps between academia and the practitioners' community. For example, few academic papers address "price oracle attacks" and "permissonless interactions", while our data suggests that they are the two most frequent incident types (15% and 10.5% correspondingly). We also investigate potential defenses, and find that: (i) 103 (56%) of the attacks are not executed atomically, granting a rescue time frame for defenders; (ii) SoTA bytecode similarity analysis can at least detect 31 vulnerable/23 adversarial contracts; and (iii) 33 (15.3%) of the adversaries leak potentially identifiable information by interacting with centralized exchanges.